9 min read
Easy ways how to query Active Directory with PowerShell
PowerShell is a powerful environment when it comes to querying information in Windows. PowerShell can be an important...
ScriptRunner Blog
If you manage Active Directory frequently – creating users, groups, troubleshooting, or maintaining domains – the PowerShell Active Directory module is a game-changer. It offers cmdlets that simplify everyday tasks and complement traditional tools. It enables faster, more effective AD management. Discover how PowerShell can level-up your AD administration experience!
To manage Active Directory with PowerShell, the Active Directory module for PowerShell must be installed. This is one of the standard Active Directory management tools and can be installed in parallel with the graphical interface tools.
On domain controllers, the PowerShell module is automatically installed with the other administration tools. On Windows 10 computers, the installation is performed using the On-demand features. The settings app is used for this purpose. The optional features can be found under "Settings App". Go to "Optional Features" and click "Add Optional Features". In the following list you’ll find "RSAT: Tools for Active Directory Domain Services and Lightweight Directory Services" (see Figure 1). The "Install" button is used to integrate the module. By installing the feature, the PowerShell module for Active Directory is also available.
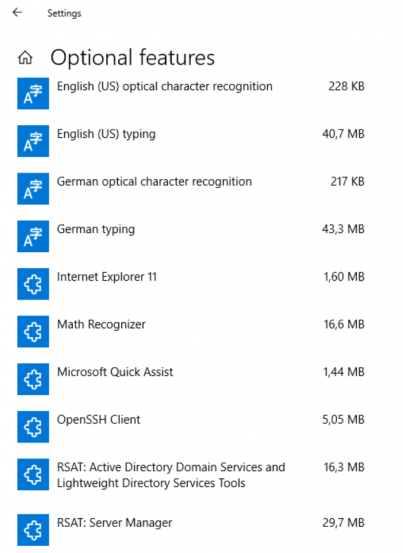
Screenshot of the settings app on Windows 10 with the "Optional Features" tab open
On servers, the installation can be done by adding the remote administration tools for Active Directory in the Server Manager or the Windows Admin Center (Figure 2). Here you can find the PowerShell module for Active Directory in the Remote Server Administration Tools Role Administration Tools AD DS- and AD LDS Tools.
On Windows servers, the Active Directory management tools can also be installed from the PowerShell. This is done by using the Install-WindowsFeature RSAT-AD-PowerShell command.

Installing Remote Administration Tools on Servers
To remotely manage a domain controller in PowerShell, the feature must be enabled on the target server. To do this, you enter the Cmdlet Enable-PSRemoting -Force in a PowerShell session on the target server (Figure 3). The command sets up the appropriate exceptions in the firewall and enables the necessary functionality. To undo the operation, use Disable-PSRemoting -Force.
If the connection does not work, you can check in the command prompt or PowerShell with winrm enumerate winrm/config/listener whether a listener with port 5985 is active and bound to all IP addresses of the server.
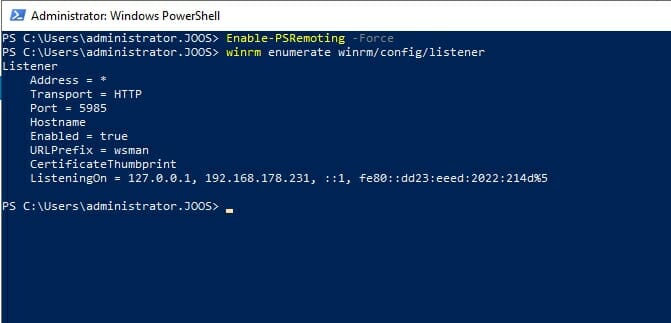
Checking the remote connection for PowerShell on Windows servers
Use the cmdlet Get-Command -Module ActiveDirectory to display all the cmdlets that can be used to manage Active Directory. The Get-Module -ListAvailable command displays all the modules. This allows you to see the names of other modules and use Get-Command to get their cmdlets (Figure 4).

Displaying the Active Directory administration cmdlets
You can also use the PowerShell to get data from individual domains. The Cmdlet Get-ADDomain is used to do this (Figure 5). The Cmdlet Get-ADForest displays information about overall structures. It can also be filtered by column and pipe to other cmdlets, such as Get-ADDomainController. The CMDlet is useful if you want to display the FSMO roles per domain. In each domain there are the three FSMO roles, which are all displayed with the following command:
Get-ADDomain | Select InfrastructureMaster, RID-Master, PDCEmulator
Displaying the data of individual AD domains using Get-ADDDomain
Schema Master and Domain Name Master are unique per AD forest. This information can be displayed again by using Get-ADForest:
Get-ADForest | Select-Object DomainNamingMaster, SchemaMaster
Operation Master roles can be moved to other domain controllers in the PowerShell. The equivalent cmdlet is
Move-ADDirectoryServerOperationMasterRole
Get-Help Move-ADDirectoryServerOperationMasterRole displays the full syntax and some examples of the cmdlet (this applies generally to all cmdlets in PowerShell).
The following cmdlets are used in the PowerShell to test domain controllers
To run the tests, passwords must be entered at various places. However, the respective cmdlet accepts them only as secure input. An example of the command is:
Test-ADDSDomainControllerInstallation -DomainName -SafeModeAdministratorPassword (Read-Host -Prompt Kennwort -AsSecureString)
After the Active Directory server role is installed, you can begin setting up the domain. To set up Active Directory, use the following cmdlet:
Invoke-Command {Install-ADDSDomainController -DomainName -Credential (Get-Credential) -ComputerName
Microsoft provides a number of cmdlets for retrieving Active Directory objects such as computers, users, or groups with PowerShell. The fastest way to get a list is to use the Get-Command Get-Ad* command. There are also many cmdlets for creating new objects. To display the list, type Get-Command New-Ad*
A list of commands to delete objects can be displayed with Get-Command Remove-Ad*. Changes to Active Directory objects are made by using Set- cmdlets. A list is of them is displayed by using Get-Command Set-Ad*.
In addition to the possibility to make settings in the graphical user interface, the deletion protection in Active Directory can also be queried and set in the PowerShell. To query the deletion protection for an object, the following command is used:
Get-ADObject ‹DN of object› -Properties ProtectedFromAccidentalDeletionThe deletion protection can be activated with:
Set-ADObject ‹DN of object› -ProtectedFromAccidentalDeletion $true
If you want to deactivate the deletion protection, you can again set the option “$false”. If no objects are to be protected but organizational units, the cmdlets Get-ADOrganizationalUnit and Set-ADOrganizationalUnit are used.
Mar 4, 2022 by Thomas Joos
PowerShell is a powerful environment when it comes to querying information in Windows. PowerShell can be an important...
Dec 10, 2021 by Thomas Joos
In PowerShell, it is relatively easy to create user accounts and groups, add users to groups or remove users from...
Nov 6, 2024 by Thomas Joos
If you manage Active Directory frequently – creating users, groups, troubleshooting, or maintaining domains – the...
Thomas Joos is a freelance IT consultant and has been working in IT since 1992. He has published more than 90 practical reference books and writes for numerous IT publications such as c’t, PC Magazin, PC Welt, IT Administrator, Computerwoche and Heise Security.